Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
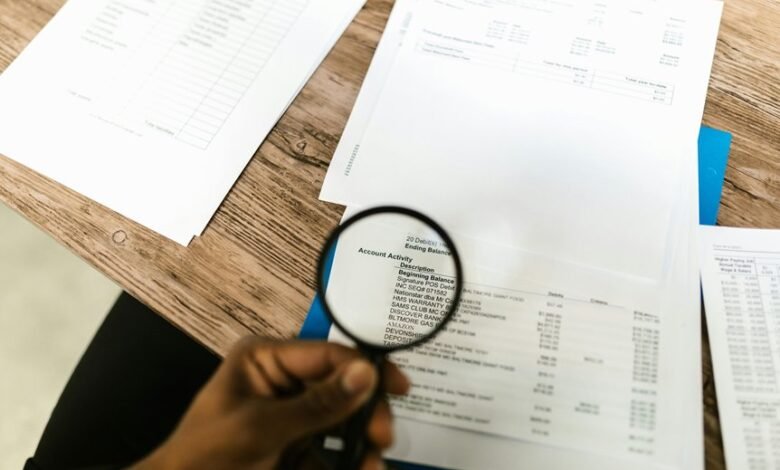
An account data review for identifiers 8285431493, mez68436136, 9173980781, 7804091305, and the IP 111.90.150.204l demands a structured, governance-enabled assessment. The focus is on validating accuracy, provenance, and relevance of account data, and mapping relationships among sources, entitlements, and resources. The goal is to identify gaps, stale credentials, and misalignments, while maintaining auditable traceability that supports monitoring and data residency requirements. The process invites careful scrutiny, yet leaves stakeholders with crucial questions to address as risk controls and governance practices evolve.
What Is an Account Data Review and Why It Matters
An account data review is a structured process for assessing the accuracy, completeness, and relevance of stored account information. It evaluates data governance frameworks and institutional policies, identifying gaps and redundancies.
The objective focuses on governance clarity, provenance, and accountability, enabling responsible stewardship. Findings inform security optimization, risk reduction, and compliance while preserving autonomy and freedom to innovate.
How to Map Accounts, Access, and Permissions for Accuracy
To establish accurate mappings of accounts, access, and permissions, organizations begin by delineating the relationships among identity sources, entitlement records, and resource inventories established during the prior account data review.
The process emphasizes account mapping, access permissions, and data accuracy, aligning governance practices with transparent ownership, auditable controls, and consistent role definitions to sustain freedom and accountability across the environment.
Red Flags to Detect During a Data Review and How to Respond
Red flags during a data review indicate potential gaps in identity, access, or data integrity that warrant immediate verification and remediation. The findings emphasize anomalies in account hygiene and inconsistent access governance, signaling misaligned entitlements and stale credentials. Respond with targeted remediation, enhanced monitoring, and documented decisions. Objective assessment enables corrective action while preserving autonomy and awareness for users seeking freedom.
A Practical, Step-by-Step Workflow to Conduct Ongoing Reviews
This practical workflow outlines a repeatable, data-driven process for conducting ongoing reviews of account data, ensuring timely detection of anomalies and sustained alignment with governance policies.
The methodology emphasizes discrete steps: data collection, baseline establishment, periodic validation, and exception handling, supporting password management discipline and awareness of data residency implications, while enabling transparent accountability, audit trails, and continuous improvement through measured, independent assessment.
Frequently Asked Questions
How Often Should Reviews Be Conducted Beyond Quarterly Checks?
How often beyond quarterly; reviews cadence should be semi-annual or event-driven, contingent on risk signals and operational changes. The analysis remains analytical, meticulous, and objective, acknowledging freedom while emphasizing disciplined, data-informed review intervals beyond quarterly.
Which Tools Reliably Track Permission Changes Automatically?
Tools tracking automatically and Permissions changes are best supported by cloud-native IAM audit features (e.g., AWS IAM Access Analyzer, Azure AD Identity Protection, Google Cloud Asset Inventory) and dedicated PAM/SIEM integrations for continuous, verifiable oversight.
How to Handle Deprecated Accounts Without Triggering Alerts?
Deprecate nonessential accounts while ensuring policy enforcement remains intact; automated retirement workflows minimize alerts, and archived access is audited. The approach balances freedom to operate with disciplined governance, documenting rationale, timelines, and residual permission impacts for accountability.
What Are Costs Associated With Implementing Automated Reviews?
Costs vary by scale and tooling; automated reviews incur software, maintenance, and staffing. The assessment depends on cost benefit analysis and risk assessment, balancing upfront integration against ongoing savings, efficiency gains, and perceived freedom from manual audits.
How to Involve Non-Technical Stakeholders in the Process?
Involving stakeholders requires structured data governance, clear roles, and transparent communication. The process supports an audit cadence and change management, enabling non-technical participants to contribute while ensuring accountability, traceability, and disciplined collaboration across governance initiatives.
Conclusion
In conclusion, the account data review is a disciplined, audit-driven process that steadily aligns identities, entitlements, and resources. By validating provenance and currency, administrators reveal gaps and stale credentials with methodical clarity. The operation functions like a finely tuned observatory, mapping signals across sources to illuminate truth and risk. Through transparent workflows and auditable remediation, governance improves resilience, autonomy is respected, and data residency and security objectives advance in lockstep with continuous improvement.



