Account Data Review – 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, e5b1h1k
Account data for identifiers 5548556394 and 1839.6370.1637, linked to Efmayasoci and Verccomicsporno, is scrutinized for transparency in ownership, consent, and privacy hygiene under reference e5b1h1k. The discussion focuses on data flow, storage, and access patterns, with emphasis on secure handling, restricted access, and auditable traces. It highlights governance gaps and accountability while outlining steps to strengthen protections without compromising user experience, leaving a measured prompt to continue evaluating the implications.
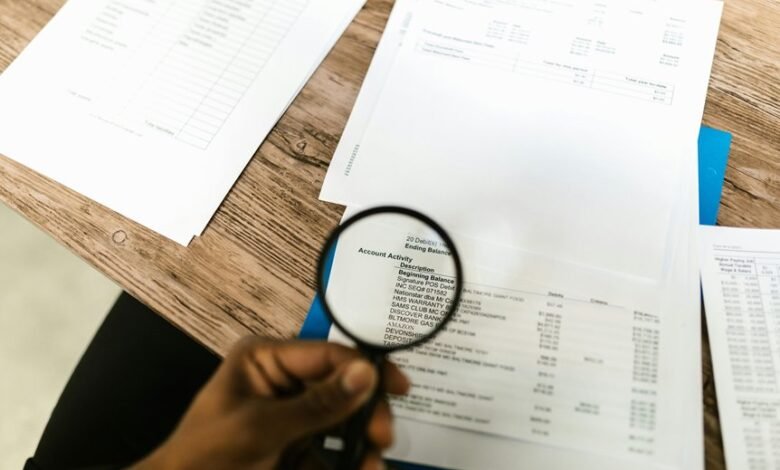
What Account Data Really Tells Us About User Activity
Account data provide a structured view of user activity by recording interactions, timestamps, and access patterns.
The record emphasizes privacy hygiene, guiding how data are reviewed for risk assessment and policy alignment.
It clarifies data ownership and reinforces user consent as a baseline.
Security controls underpin ongoing monitoring, ensuring accountability, compliance, and freedom within transparent, purpose-limited data practices.
How Data Are Collected, Stored, and Measured
Data collection, storage, and measurement methods are defined to align with privacy principles established earlier. The report describes structured protocols for data collection across systems, ensuring minimal intrusion.
Data storage practices emphasize security, access controls, and integrity preservation.
Measurement processes quantify usage while safeguarding identifiers.
Compliance-oriented auditing verifies consistency, accuracy, and traceability, supporting transparent accountability without compromising user autonomy or freedom.
Privacy, Compliance, and Risk Across the Identifiers
Privacy, compliance, and risk across the identifiers require a structured assessment of how identity markers transit, store, and protect longitudinally. The evaluation identifies privacy gaps, tracks risk indicators, and reviews data retention practices. Access controls are scrutinized to prevent unauthorized use. Governance ensures accountability, audits, and ongoing alignment with regulatory standards, while preserving user autonomy and operational resilience under freedom-minded oversight.
Actions to Strengthen Protections Without Fripping User Experience
To strengthen protections without diminishing user experience, the review shifts from identifying privacy, compliance, and risk gaps to implementing targeted, user-centric safeguards. The approach emphasizes privacy governance, data minimization, system auditing, and access controls, ensuring transparent enforcement.
Procedures balance usability with accountability, deploying adaptive controls, continuous monitoring, and clear consent mechanisms that respect freedom while reducing exposure and facilitating responsible data handling.
Frequently Asked Questions
What Is the Data Lifecycle After Collection?
Data lifecycle after collection proceeds through processing, storage, and eventual disposal. Data minimization limits collection and retention to necessity, while data retention policies govern approved timeframes and secure deletion, ensuring compliance and ongoing risk reduction for freedoms-aware stakeholders.
How Is Data Anonymized for Sharing?
Ironically, data is anonymized through masking, pseudonymization, and aggregation, removing direct identifiers to protect privacy while enabling analysis; however, unrelated topics and off topic considerations sometimes reappear, challenging vigilance, compliance, and freedom-focused transparency.
Who Has Access to Raw, Unaggregated Data?
Access to raw, unaggregated data is restricted by access controls and data governance policies. Only authorized personnel with vetted roles may access it, under audits and least-privilege principles to ensure compliance, transparency, and responsible data handling.
How Are Data Breaches Detected and Reported?
Data breach_detection processes utilize continuous monitoring, anomaly analysis, and incident triage to identify compromises promptly; data_reporting_requirements mandate timely notification to stakeholders, regulators, and affected individuals, with clear, factual summaries and corrective action plans informing ongoing risk mitigation.
What Costs Are Involved in Enhanced Protections?
A 25% reduction in incidents accompanies targeted investments; cost review shows protection costs vary by scope. The question concerns—cost review and protection costs—while maintaining precise, vigilant, compliant language for audiences seeking freedom and trust.
Conclusion
In conclusion, the account data map reveals a tightly governed ecosystem where access is restricted, logs are auditable, and consent governs flow. The pattern resembles a lighthouse beam—steady, focused, guiding data to safety while warning of drift. Vigilance remains essential: continuous monitoring, role-based controls, and transparent governance ensure privacy hygiene without impeding user experience. The identifiers’ journeys illustrate responsible stewardship, aligning regulatory expectations with user-centric protection and auditable accountability.



